Have issues with slow loading times for right click, open with menu on OSX?
Copy and paste the below to resolve –
/System/Library/Frameworks/CoreServices.framework/Versions/A/Frameworks/LaunchServices.framework/Versions/A/Support/lsregister -kill -seed -r -f -v -domain local -domain user -domain system
Ignore any errors, as it re-removes and re-registers registered context menu’s – once completed, right click menu’s will be back to their fast speed.
I bought a Phicomm R1 Speaker for 150RMB delivered, its supposed to have Wifi and a config app, but the App registration is apparently broken.
The Phicomm R1 speaker has Android installed, unfortunately the configuration app for the speaker is no longer working as noted, so you can only use Bluetooth unless you hack it (Bluetooth is available via a triple press of the top button).
For some crazy reason, the speaker has a fairly decent cpu, and is running Android (albeit without a display, which is annoying, but not completely unfixable); we can connect via adb.
Download adb tools here – https://www.xda-developers.com/install-adb-windows-macos-linux/ and stick in your path.
Set the speaker to Wifi (long press of the top button), and connect to the Phicomm_R1_xxx network.
Mine setup a network on 192.168.43.0/24, with a gateway of 192.168.43.1
adb connect 192.168.43.1:5555
adb shell ls -al
drwxr-xr-x root root 2016-01-21 16:50 acct
lrwxrwxrwx root root 2016-01-21 16:50 bcm4329_cybertan.hcd -> /etc/bluez/bcm432x/BCM4329B1_002.002.023.0389.0000_Cybertan-Foxconn_Cls2_extLNA_EDRmaxInputLev+PeakDEVM_NT.hcd…
-rw-r--r-- root root 148936 1970-01-01 08:00 rk30xxnand_ko.ko.3.10.0
drwx------ root root 2018-04-28 10:50 root
-rw-r--r-- root root 252134 1970-01-01 08:00 vcodec_service.koYup, that worked!
lrwxrwxrwx root root 2016-01-21 16:50 vendor -> /system/vendor
Ok, so we can see the thing at least! Lets get some screen viewing software installed. I’m on OSX, so its a simple brew install..
This seems to work reasonably well – https://github.com/Genymobile/scrcpy
brew install scrcpy
#load ADB first as above on the default unconfigured wifi ip
adb connect 192.168.43.1:5555
scrscpy
You should now be able to see the device display, and the internal app called Pandora. The pandora app is a rather useless one – it basically doesn’t work. So ignore..
We need to install other tools.
#allow any app install
adb shell settings put secure install_non_market_apps 1
Next up, configure wifi on the thing!
#install adb wifi tool
wget https://github.com/steinwurf/adb-join-wifi/releases/download/1.0.1/adb-join-wifi.apk
adb push adb-join-wifi.apk /data/local/tmp/adb-join-wifi.apk
adb shell /system/bin/pm install -t /data/local/tmp/adb-join-wifi.apk
#change YOURSSID, and YOURWIFIPASS as appropriate..
adb shell am start -n com.steinwurf.adbjoinwifi/com.steinwurf.adbjoinwifi.MainActivity -e password_type WPA -e ssid YOURSSID -e password YOURWIFIPASS
It will hopefully setup the wifi. You’ll need to wait for it to ‘timeout’ and tell you wifi setting failed; it will then connect to your normal wifi as set above.
Once on your ‘normal’ wifi, you can adb connect again to the normal ip.
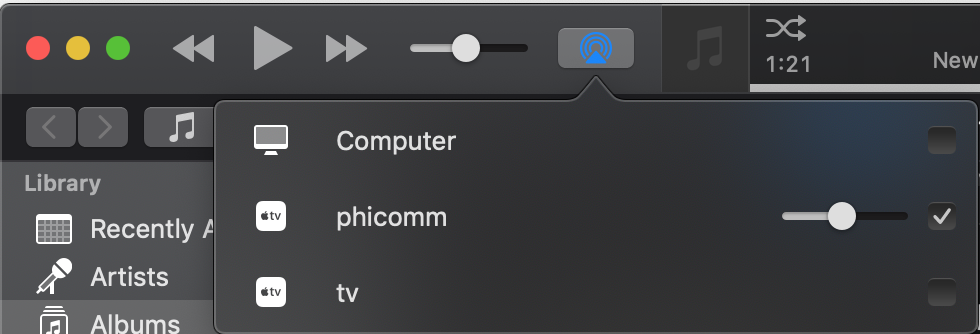
I installed airpin.apk to setup Airplay, now I can connect to the speaker in iTunes, and play. Good enough!
It can be downloaded here – http://www.waxrain.com/product_en.html
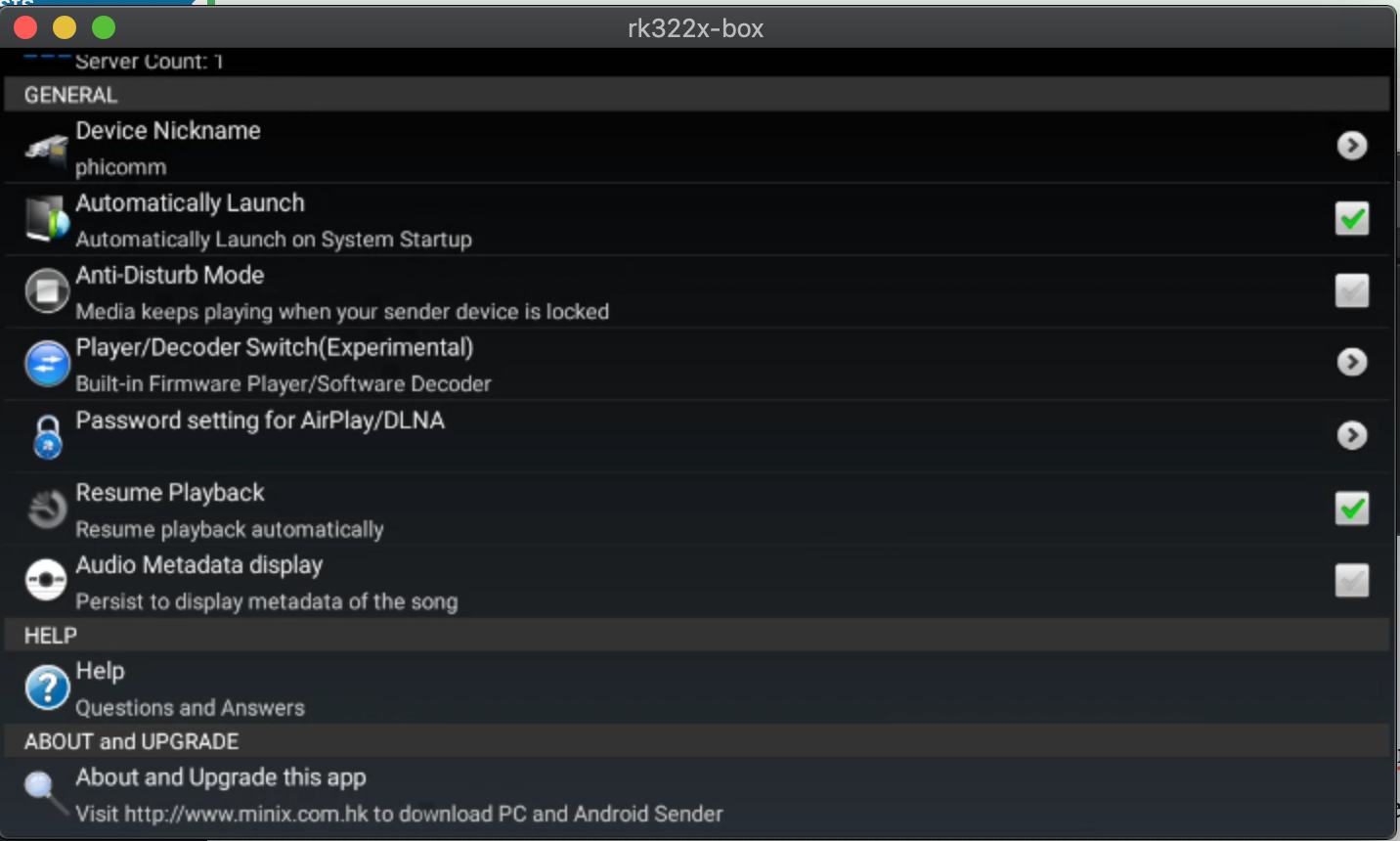
Install in a similar manner as other apk’s, then use screen mirroring to config the name.
I called mine phicomm
#copy and install airpin APK
adb push AirPin.apk /data/local/tmp/AirPin.apk
adb shell /system/bin/pm install -t /data/local/tmp/AirPin.apk
#run the screen mirroring to configure directly on the device
scrcpy
You can go further and remove the Xiao Xun (小讯) listening software, and install something else, but I haven’t bothered (yet). Mine is still unconfigured.
This is detailed in Chinese over here –
https://www.right.com.cn/forum/thread-855587-1-5.html
6
Mail Server Updates
The mail software has been completely revamped to support additional security precautions.
Failed logins will be blocked by ip address for 1 hour. (5 fails to trigger a 1hr block)
Senders can only send mail from their authenticated email address.
Outgoing mail is now also inspected for spam, if tests fail, sending will fail.
DKIM signing is now possible, we are in the process of implementation and testing.
SSL connections are now set to a minimum of TLS1.2 and 2048bit encryption, as per internet standards.
Support for connecting to servers still using old insecure protocols has been deprecated (i.e. not supported anymore).
The protocol insecurity issue is explained in more detail here –
https://weakdh.org
This has impacted some deliveries to outdated servers, which still use outdated software.
We can resolve these issues on a case by case basis if you forward support the relevant bounce messages.
If you see bounce messages with errors similar to this –
SSL routines:tls_process_ske_dhe:dh key too small;
SSL routines:ssl_choose_client_version:unsupported protocol;
The recipients server’s SSL key setup (the key they use for encryption for their mail server) is an issue.
Their keys are too small, and vulnerable to eavesdropping, and ideally need to be updated, as their communications are vulnerable.
Archives
- November 2024
- November 2019
- October 2019
- August 2019
- April 2019
- February 2017
- September 2016
- June 2016
- May 2016
- September 2015
- August 2015
- June 2015
- April 2015
- December 2014
- October 2014
- September 2014
- July 2014
- June 2014
- April 2014
- October 2013
- July 2013
- May 2013
- April 2013
- March 2013
- January 2013
- December 2012
- October 2012
- August 2012
- July 2012
- June 2012
- May 2012
- April 2012
- March 2012
- December 2011
- November 2011
- October 2011
- September 2011
- July 2011
- May 2011
- April 2011
- March 2011
- February 2011
- January 2011
- December 2010
- November 2010
- October 2010
- September 2010
- August 2010
- July 2010
- June 2010
- May 2010
- April 2010
- March 2010
- February 2010
- January 2010
- December 2009
- November 2009
- October 2009
- May 2009
- April 2009
- March 2009
- February 2009
- January 2009
- December 2008
- November 2008
- October 2008
- September 2008
Categories
- Apple
- Arcade Machines
- Badges
- BMW
- China Related
- Cool Hunting
- Exploits
- Firmware
- Food
- General Talk
- government
- IP Cam
- iPhone
- Lasers
- legislation
- MODx
- MySQL
- notice
- qmail
- requirements
- Reviews
- Service Issues
- Tao Bao
- Technical Mumbo Jumbo
- Things that will get me censored
- Travel
- Uncategorized
- Useful Info


